Critical TP-Link Router Vulnerability CVE-2024-21833 Puts Networks at Risk
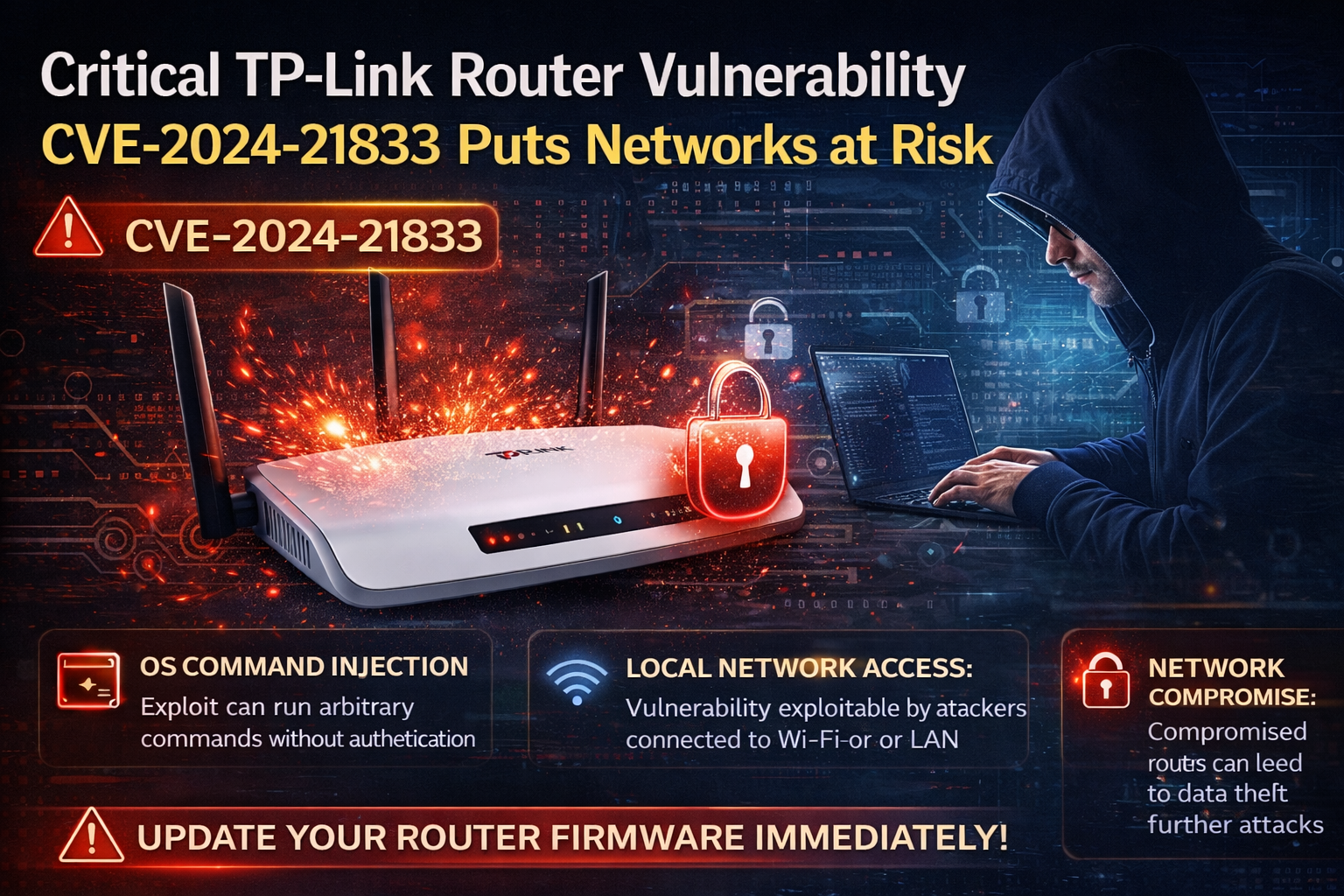
A critical security vulnerability affecting TP-Link Routers is drawing renewed attention as researchers warn of increasing exploitation attempts that could allow attackers to gain control over devices and compromise entire networks.
The flaw, tracked as CVE-2024-21833, impacts multiple TP-Link router and mesh models, including Archer and Deco series devices. It is classified as an OS command injection vulnerability, enabling attackers to execute arbitrary commands on affected systems without authentication under certain conditions.
Security experts note that the vulnerability can be exploited by attackers with access to the local network, such as through Wi-Fi or LAN connections. Once inside, malicious actors can run system-level commands, potentially leading to full device compromise, data interception, and lateral movement across connected systems.
The issue stems from improper input validation in the router’s web management interface, where user-supplied data is not adequately sanitized before being processed by the system. This allows attackers to inject and execute unauthorized commands directly on the device’s operating system.
The vulnerability carries a high severity rating, with a CVSS score of 8.8, reflecting its potential impact on confidentiality, integrity, and availability. Affected firmware versions include several widely used consumer and enterprise networking products, increasing the overall risk exposure.
Researchers warn that compromised routers can be used for a range of malicious activities, including traffic interception, credential harvesting, and launching further attacks within a network. In large-scale scenarios, such vulnerabilities can also be leveraged to build botnets or support coordinated cyberattacks.
TP-Link has released firmware updates to address the issue, and users are strongly advised to upgrade their devices immediately. Additional mitigation measures include disabling remote management, using strong administrative passwords, and isolating critical systems from unsecured networks.
The incident highlights the ongoing risks associated with IoT and networking devices, where outdated firmware and weak security configurations continue to provide entry points for attackers.