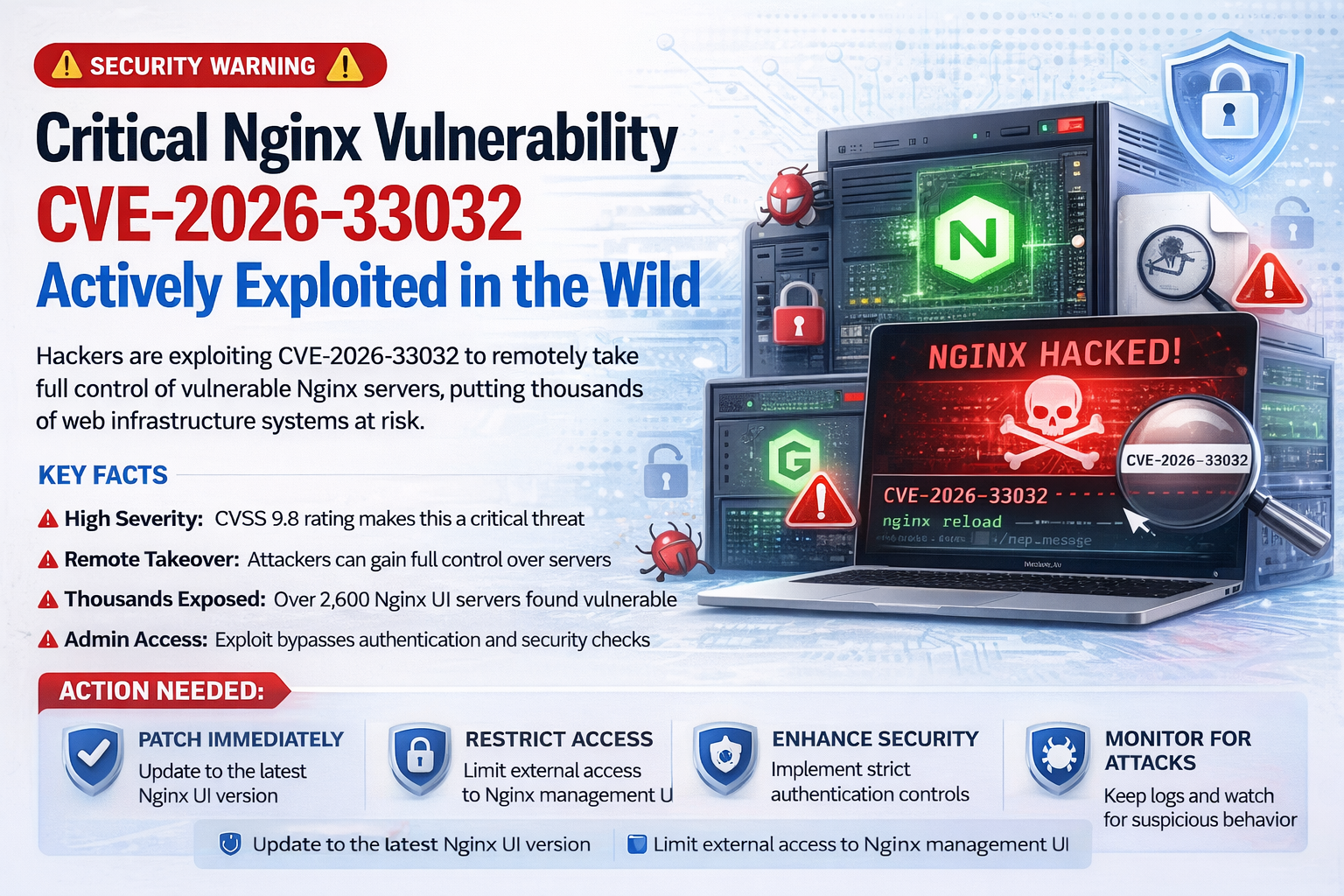
A critical vulnerability in the Nginx UI management tool is being actively exploited by hackers, exposing thousands of servers worldwide to potential takeover and data compromise.
Tracked as CVE-2026-33032, the flaw allows unauthenticated remote attackers to gain full control over affected Nginx servers by exploiting a misconfigured endpoint in the software’s Model Context Protocol (MCP) integration. Security researchers warn that this vulnerability can be leveraged using simple HTTP requests, making exploitation relatively easy and highly dangerous.
The issue stems from an authentication bypass in the /mcp_message endpoint, which lacks proper security checks while still providing access to powerful administrative functions. In default configurations, the system’s IP whitelist is effectively open, allowing any external attacker to interact with the endpoint without credentials.
Once exploited, attackers can perform a wide range of malicious actions, including modifying or deleting server configurations, restarting services, intercepting web traffic, and deploying backdoors. This level of access effectively results in a complete takeover of the Nginx server environment.
Security researchers have identified more than 2,600 internet-exposed instances of Nginx UI, increasing the risk of widespread exploitation. The availability of proof-of-concept (PoC) exploit code further amplifies the threat, as it lowers the barrier for attackers to launch automated attacks at scale.
The vulnerability carries a critical severity rating (CVSS score of 9.8), reflecting its potential impact on confidentiality, integrity, and availability of affected systems.
Experts warn that compromised servers could be used for traffic interception, credential harvesting, or as entry points into larger networks, posing serious risks to organizations relying on Nginx for web infrastructure.
Although patches have been released in newer versions, many systems remain unpatched or exposed, making them prime targets for ongoing attacks. Security professionals are urging administrators to update immediately, restrict access to management interfaces, and implement strict authentication controls to mitigate the risk.