Mirai Variant Nexcorium Exploits IoT Devices to Launch Large-Scale DDoS Attacks

A new variant of the notorious Mirai botnet, dubbed Nexcorium, is actively exploiting vulnerabilities in internet-connected devices, allowing attackers to hijack systems and launch large-scale distributed denial-of-service (DDoS) attacks.
Security researchers report that the campaign primarily targets TBK digital video recorder (DVR) devices by exploiting CVE-2024-3721, a command injection vulnerability affecting specific DVR models. By abusing this flaw, attackers can execute malicious commands remotely and deploy malware onto vulnerable devices.
Once compromised, the devices are turned into bots within a growing botnet infrastructure. The attackers use a downloader script to fetch and execute malware payloads tailored for multiple system architectures, including ARM, MIPS, and x86, enabling widespread infection across diverse IoT environments.
The Nexcorium malware shares core characteristics with traditional Mirai variants, including modular components such as scanners, watchdog processes, and attack engines. These features allow it to maintain persistence on infected systems, evade detection, and receive commands from a central command-and-control (C2) server to execute coordinated DDoS attacks.
Researchers also observed that the malware incorporates additional exploits, including older vulnerabilities targeting devices like Huawei routers, as well as a built-in list of default credentials to brute-force access via Telnet. This multi-pronged approach significantly increases the botnet’s ability to spread rapidly across poorly secured networks.
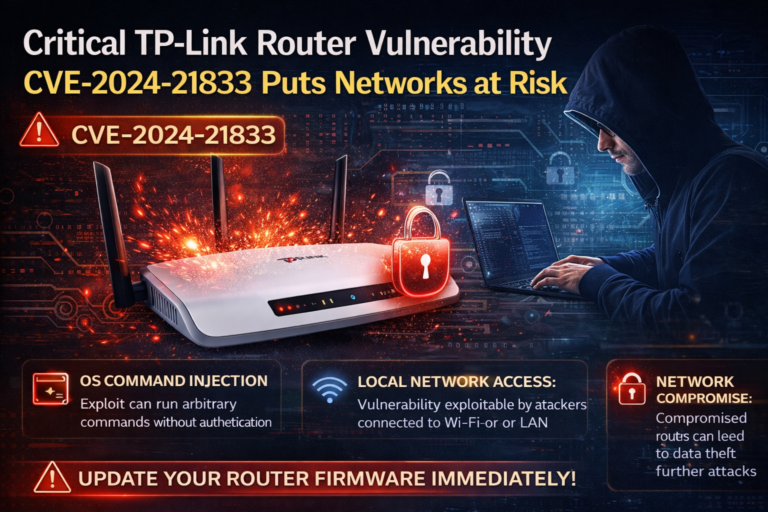
Notably, attackers are also targeting end-of-life TP-Link routers with known vulnerabilities, further expanding the attack surface. Many of these devices remain unpatched or unsupported, making them easy targets for compromise.
The campaign underscores a persistent trend in cybersecurity: IoT devices continue to be highly vulnerable due to weak security configurations, outdated firmware, and lack of regular patching. Once infected, these devices can be weaponized at scale to disrupt online services, overwhelm networks, and support broader cyberattack operations.
Experts warn that as attackers increasingly automate exploitation and leverage known vulnerabilities, organizations and individuals must prioritize securing IoT devices by updating firmware, disabling default credentials, and restricting unnecessary network exposure to mitigate the risk of botnet-driven attacks.